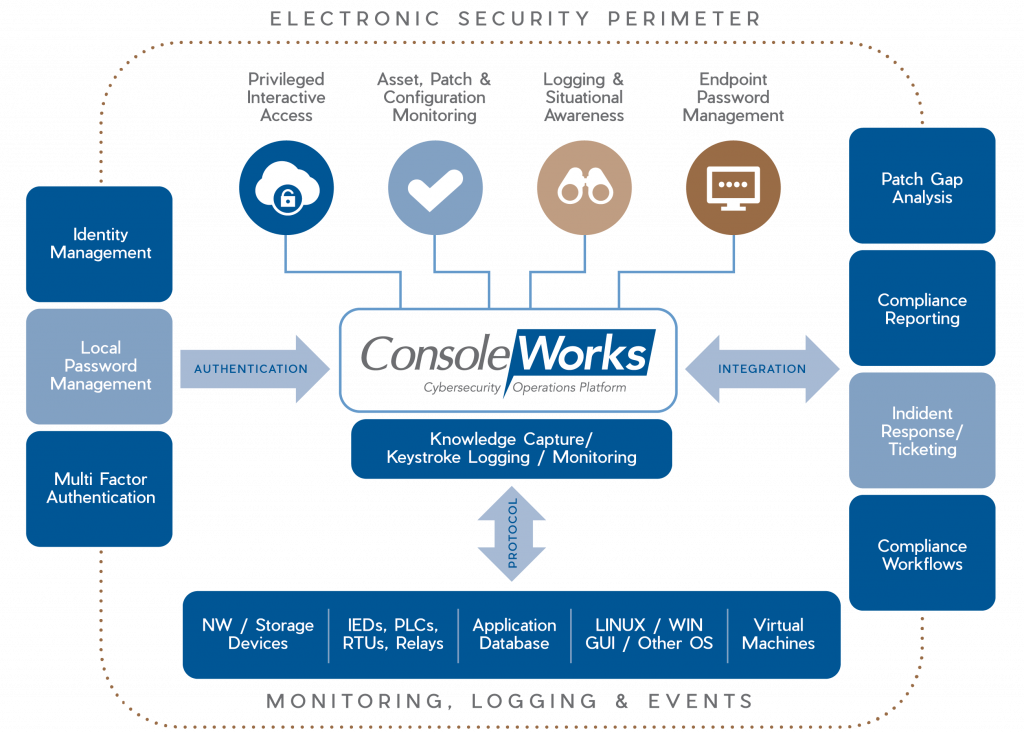
In the relentless battle against the ever-evolving landscape of cyber threats, collaboration between cybersecurity solution providers and government agencies is paramount. This paper shines a spotlight on the partnership between ConsoleWorks, a leading Zero Trust cybersecurity platform, and the Cybersecurity and Infrastructure Security Agency (CISA) Joint Cyber Defense Collaborative (JCDC). The focus of this collaboration encompasses ConsoleWorks’ pioneering features, specifically Secure Remote Access with a true protocol break, ConsoleWorks REACT (Risk Evaluation and Assessment for Cyber Threats), Log correlation and event management, and the indispensable role of continuous monitoring with the Baseline Configuration Management (BCM) feature. More about what the CISA JCDC partnership encompasses can be found here: CISA JCDC
ConsoleWorks: Pioneering Zero Trust Secure Remote Access with a Protocol Break
ConsoleWorks stands as an indispensable ally in the realm of cybersecurity, offering a suite of robust features designed to ensure secure remote access to critical infrastructure. In an era where remote work is the norm, ConsoleWorks’ Protocol Break capabilities take center stage. This innovative approach places a strong emphasis on controlled and encrypted connections, effectively acting as a “man-in-the middle” monitor for any unauthorized access attempts. ConsoleWorks permits authorized personnel to access critical systems without compromising security, fortifying the defenses against potential cyber threats.
ConsoleWorks REACT: Comprehensive Risk Evaluation and Assessment
The complex and ever-changing cyber threat landscape requires a comprehensive approach to risk evaluation and assessment. ConsoleWorks employs a state-of-the-art strategy known as ConsoleWorks REACT (Risk Evaluation and Assessment for Cyber Threats). This proactive approach aligns seamlessly with JCDC’s mission of collective defense. ConsoleWorks conducts continuous risk assessments, assessing vulnerabilities and monitoring configuration changes for situational and operational awareness. Such a strategy empowers organizations to identify potential threats before they escalate into significant security incidents, staying ahead of the evolving threat landscape.
Continuous Monitoring with BCM: Enhancing Cyber Resilience
ConsoleWorks bolsters its capabilities through Baseline Configuration Management (BCM), a feature that plays an instrumental role in continuous monitoring. BCM ensures that the configuration of critical assets remains aligned with established and authorized baselines. By continuously monitoring and managing configuration changes, BCM not only participates in risk evaluation but also mitigates mis operations and provides invaluable assistance in incident response and recovery. It serves as the guardian of operational integrity.
CISA JCDC remote monitoring and management cyber-defense-plan
ConsoleWorks Zero Trust Cybersecurity Platform for CISA JCDC
The collaboration between ConsoleWorks and CISA JCDC amplifies the capabilities of Secure Remote Access, ConsoleWorks REACT, and BCM. By integrating real-time threat intelligence from JCDC, ConsoleWorks’ cybersecurity platform becomes even more dynamic and adaptive, preemptively thwarting unauthorized access attempts. In partnering with JCDC’s, and through collaborative efforts, ConsoleWorks REACT provides a template for mitigating an organizations risk in real-time. Meanwhile, BCM actively contributes to risk mitigation, ensuring operational integrity, and expediting incident response and recover by tracking and monitoring “known-good” asset configurations for unauthorized changes and library vulnerabilities.
Enhanced Incident Response and Recovery
In the event of a cyber incident, ConsoleWorks plays a pivotal role in incident response and recovery. Its continuous monitoring and session recording capabilities offer a crucial forensic toolset. When an incident occurs, organizations can rely on ConsoleWorks’ recorded data to investigate the incident’s root cause, identify compromised systems, and assess the extent of the breach. This invaluable information accelerates the incident response process, reducing downtime and minimizing the impact of cyberattacks. Furthermore, with asset “known-good” running state baselines that are stored within ConsoleWorks, the restoration of an asset can coincide with the incident response operations.
Comprehensive Compliance and Reporting
ConsoleWorks is not only a robust cybersecurity platform but also a compliance enabler. It automates compliance checks and generates audit-ready reports, ensuring that organizations meet regulatory requirements, effortlessly. This feature is particularly crucial for critical infrastructure sectors that must adhere to stringent compliance standards. Through ConsoleWorks, organizations can maintain compliance without the burden of manual checks and reporting.
Scalability and Integration
ConsoleWorks is designed with scalability and integration in mind. As organizations grow and their cybersecurity needs evolve, ConsoleWorks adapts. It seamlessly integrates with existing security tools, creating a cohesive security ecosystem. Whether an organization operates on a small scale or a large enterprise level, ConsoleWorks scales to meet the demands of the ever-expanding threat landscape.
Conclusion
In a dynamic cyber threat landscape, partnerships such as the one between ConsoleWorks and CISA JCDC are the linchpins in safeguarding critical infrastructure and data. The emphasis on Secure Remote Access with protocol break, the adoption of ConsoleWorks REACT for comprehensive risk evaluation and assessment, logging and event correlation, and the inclusion of BCM for continuous monitoring underscore ConsoleWorks’ commitment to providing a holistic cybersecurity platform. This collaboration bolsters these features, demonstrating a proactive approach in addressing emerging threats, and increases the reliability of the organizations operations.
Together, they exemplify the potential of cooperation and innovation to mitigate the ever-evolving cyber threat landscape, securing the digital future of organizations and critical infrastructure. As organizations navigate the complex cybersecurity terrain, ConsoleWorks and JCDC stand as guardians, offering a beacon of resilience in an interconnected world, ensuring the secure, uninterrupted operation of critical infrastructure assets.
For organizations eager to explore the capabilities of ConsoleWorks and witness firsthand how it can strengthen their cybersecurity posture, we extend an invitation to contact us. Our dedicated team is poised to provide further information, address inquiries, and arrange a live demonstration of our solution. Contact us today to embark on a journey towards enhanced cybersecurity, proactive threat mitigation, and a fortified digital future. Together, we can navigate the ever-evolving cyber landscape with confidence and resilience.
[SCHEDULE A DISCUSSION AND DEMO]