What is Privileged Interactive Access in ConsoleWorks? Privileged Interactive access management is a specific subset of access management where the interfaces being managed have a very high level of privilege associated with them. One of the most common examples of a privileged interface is an account on an operating system.
Privileged access occurs every day – for example, to manage both IT & OT operations. Both groups are accessing interfaces with extremely high privileges where mistakes can directly result in service disruption, compliance failure, and data breaches. They both need to be effectively managed to prevent security risk to the business.
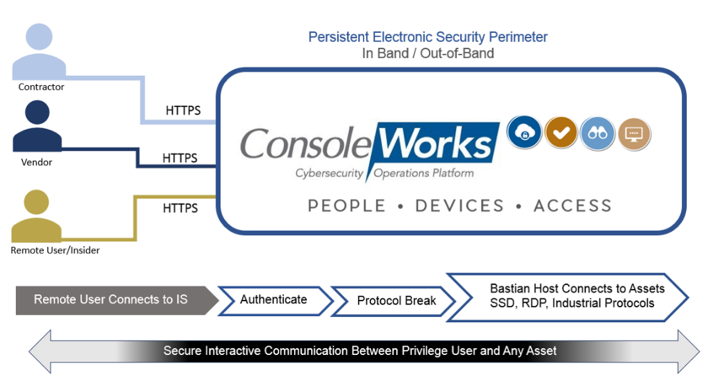
ConsoleWorks offers organizations a single tool that can manage all privileged access in the organization. From operating systems to configuration ports, ConsoleWorks can control access, enforce permission models, and record (down to the keystroke) all privileged user activity for virtually any asset in the IT/OT environment.
Solution Brief – Privileged Interactive Access
ConsoleWorks provides a protocol break between the assets and the people.