Project Aims to Help Energy Providers Monitor, Manage, and Secure Their Assets
ForeScout Technologies, Tripwire, Dragos, Splunk, KORE Wireless, TDi Technologies, FoxGuard Solutions, and Veracity Industrial Networks have joined the National Cybersecurity Center of Excellence (NCCoE) as technology collaborators in the Energy Sector Asset Management (ESAM) Project.*
In response to a call in the Federal Register, these companies submitted capabilities that aligned with desired solution characteristics listed in the project description. These technology collaborators were extended a cooperative research and development agreement (CRADA; see example), allowing them to participate in a consortium where they will contribute expertise and hardware or software to help refine a reference design and build an example standards-based implementation.
As part of this collaboration, the NCCoE will compose and release a publicly available National Institute of Standards and Technology (NIST) Cybersecurity Practice Guide (Special Publication 1800 series), which will document the reference design and help organizations in the energy sector effectively identify, control, and monitor their operational technology (OT) assets.
NCCoE Focuses on Critical Infrastructure Through Operational Technology Assets
OT /Industrial Control Systems (ICS) are used in the energy sector and other critical infrastructure sectors to manage industrial operations. Disruptions to OT/ICS assets can result in economic loss and interruption of critical services to millions of consumers. Energy providers recognize the need to improve their OT asset management capabilities, especially for remote assets, to mitigate vulnerabilities and opportunities for malicious attacks.
The project will aim to address the following characteristics of asset management:
- Asset Discovery: establishment of a full baseline of physical and logical locations of assets
- Asset Identification: capture of asset attributes, such as manufacturer, model, operating system, internet protocol (IP) addresses, media access control addresses, patch-level information, and firmware versions
- Asset Visibility: continuous identification of newly connected or disconnected devices, and IP (routable and non-routable) and serial connections to other devices
- Asset Disposition: the level of criticality (high, medium, or low) of an asset, its relation to other assets within the OT network, and its communication (including serial) with other devices
- Alerting Capabilities: detection of a deviation from the expected operation of assets
Collaborating on an Advanced Strategy
In partnership with the selected technology collaborators, the NCCoE will implement the collaborators’ commercially available products in a laboratory environment to build a standards-based, modular, end-to-end example solution that will address the security challenges of OT asset management for the energy sector.
Business Benefits
The example solution for this project aims to provide the following business benefits:
- reduces cybersecurity risk and potentially reduces impact to safety and operational risk such as power disruption
- develops and executes a strategy that provides continuous OT asset management and monitoring
- enables faster responses to security alerts through automated cybersecurity event/attack capabilities
- implements current cybersecurity standards and best practices while maintaining the performance of energy infrastructures
How to Participate
Interested parties are encouraged to engage with us through our project web page.
If you have additional comments or questions or would like to join the community of interest that is helping guide this project and provide feedback, please email us at Energy_nccoe@nist.gov.
*Certain commercial entities, equipment, products, or materials may be identified to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by NIST or NCCoE, nor is it intended to imply that the entities, equipment, products, or materials are necessarily the best available for the purpose.
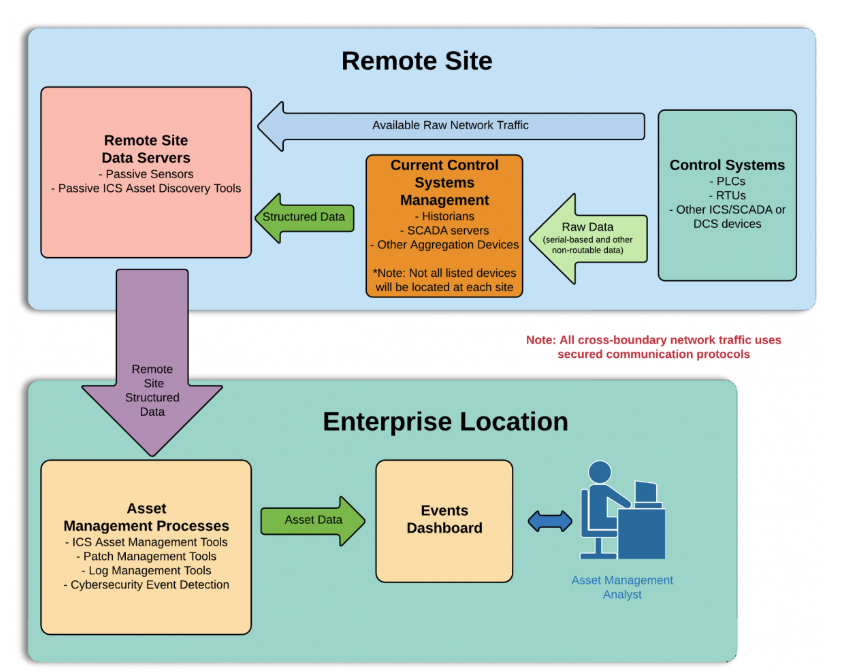
Energy Sector Asset Management Architecture
This diagram depicts the proposed high-level architecture to help improve an energy provider’s asset management capabilities. This architecture demonstrates a single physically remote site that contains the sensor and remote monitoring technologies specific to this project. This individual remote site is modular and can be scaled to represent other remote locations that feed information back to a single centralized enterprise location. There may be more than one remote site in this build.